I was reminded of this article yesterday where a few years ago there was a malicious download made available on kcna.kp: https://www.pcworld.com/article/2868436/north-korean-official-news-agency-site-serves-malware.html
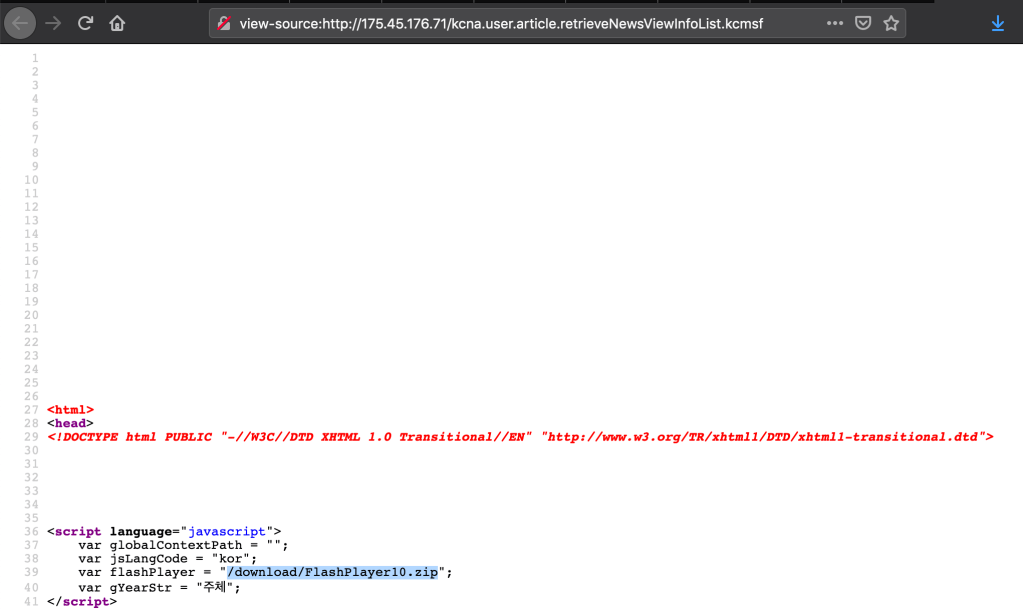
Despite this being discovered a few years ago, you can still find references to the file in the source of the site
The one thing that’s interesting is that part of the URL has exploit in it, but as the article notes it could just be a translation error. One of the things that I found interesting looking at the source of the page is that there are hidden links for check_system_password and admin_login
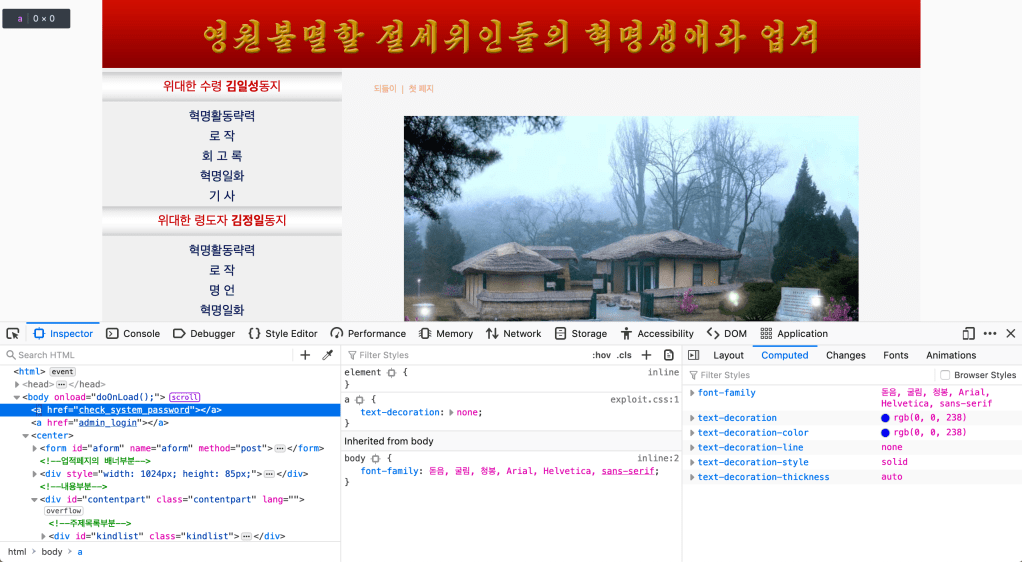
There’s also a directory siteFiles/exploit but I saved a few of the files and sent them to VirusTotal doesn’t look like there is anything suspicious:
Also based on the dates for some of the files it looks like they’ve been known for at least a few years.
Now these two links don’t load anything and they aren’t visible but archive.org captured these pages back in 2015 and it looks like it just causes the page to continuously reload:
https://web.archive.org/web/20150703061753id_/http://kcna.kp/admin_login
Looking through some of the site I also found similar references where there are links in the code but not visible anywhere on the site:
/system_admin_login_class
/check_db_password
/\\\check_system_password
Neither of those pages load but just found it interesting that they these links are hidden in the code but not visible anywhere on the site that I’ve been able to find.