Found this posted on twitter a few days ago, not yet listed on dprkportal.kp
Author: nick
Re-Signing North Korean Android Apps
In case you run into a similar problem that I ran into on getting apks off DPRK phones and not being able to run them on other devices. Here’s the steps for re-signing
apktool d -r -s application.apk
cd ./application/original/META-INF
rm -f *
cp ./application/dist/application.apk
jarsigner -verbose -sigalg SHA1withRSA -digestalg SHA1 -keystore my-release-key.keystore application.apk alias_name
zipalign -v 4 application.apk application_aligned.apk
If needed to generate the cert for signing:
keytool -genkey -v -keystore my-release-key.keystore -alias alias_name -keyalg RSA -keysize 2048 -validity 10000
Obviously you’ll need to install apktool, jarsigner, zipalign. replace application.apk with the name of the apk that you’re working with.
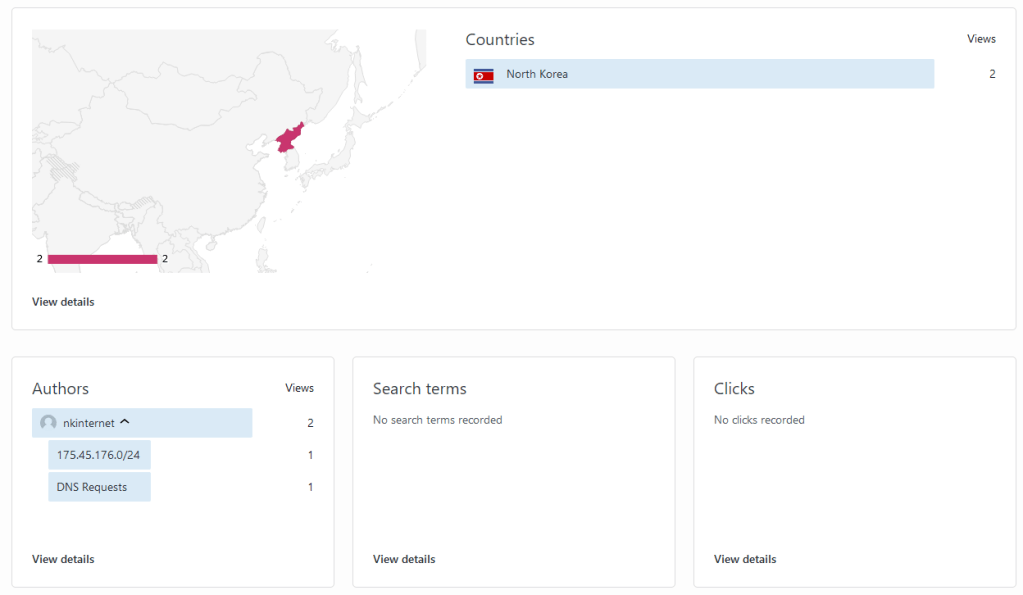
I see you North Korea creeping on my site
New IP Addresses Being Used
Looks like a bunch of domains have switched in the last few days and are now resolving to 175.45.177.10 and 175.45.177.11
North Korea Technology Advertisements – 2012
It’s Been a While and New Content Coming
I admit it’s been a while since all the excitement at the start of the year. I’m still not convinced that the person interviewed in the Wired article was responsible for the attacks, or at the very least if they were they definitely exaggerated their activity.
But, looking forward. Two things that I’ve been working on. One is taking a closer look at North Korean firewalls. The other is a list of 200 star-co.net.kp email addresses which has been an interesting list to search with. I’ll be posting some of the findings from that list.
For example I found this post on vk.com that describes the Nenara Taedongan TV factory which I haven’t seen anywhere else online. Judging based on the contact info and some of the information it appears to be something that can be reasonably trusted. https://vk.com/wall-61269228_2342?lang=en
North Korea DDoS Wrap Up
This has all been very fun to monitor but looks like it’s coming to an end with the Wired article from yesterday. One last interesting thing that I wanted to point out is that I own a domain that is very similar to a popular North Korean domain, minus the .kp tld. It didn’t hit me until a few days later but there are some interesting coincidences in the traffic that I’ve seen on that server and comparing it to the outages on the DPRK websites.
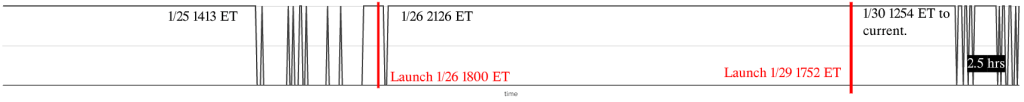
If I can re-use my graph that I created the other day right around the final outage my website that is similar to the DPRK website received over 41,000 requests in the span of a minute and a half. Specifically right around the end of the 2.5 hour gap is when I saw things spin up.
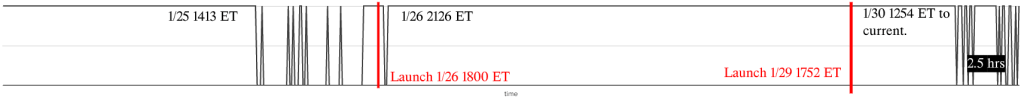
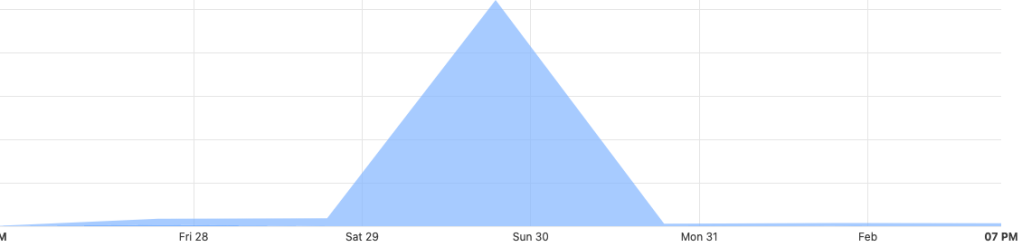
Again, attribution is incredibly difficult and not something that I want to get into at all. But it was a pretty strange coincidence that my very similar domain saw a major spike in traffic at the exact same time that the DDoS against North Korea was occurring. I don’t want to share all of the details publicly but if you are interested, and have a decent use for the data, feel free to send me an email.
North Korean Investment Opportunities
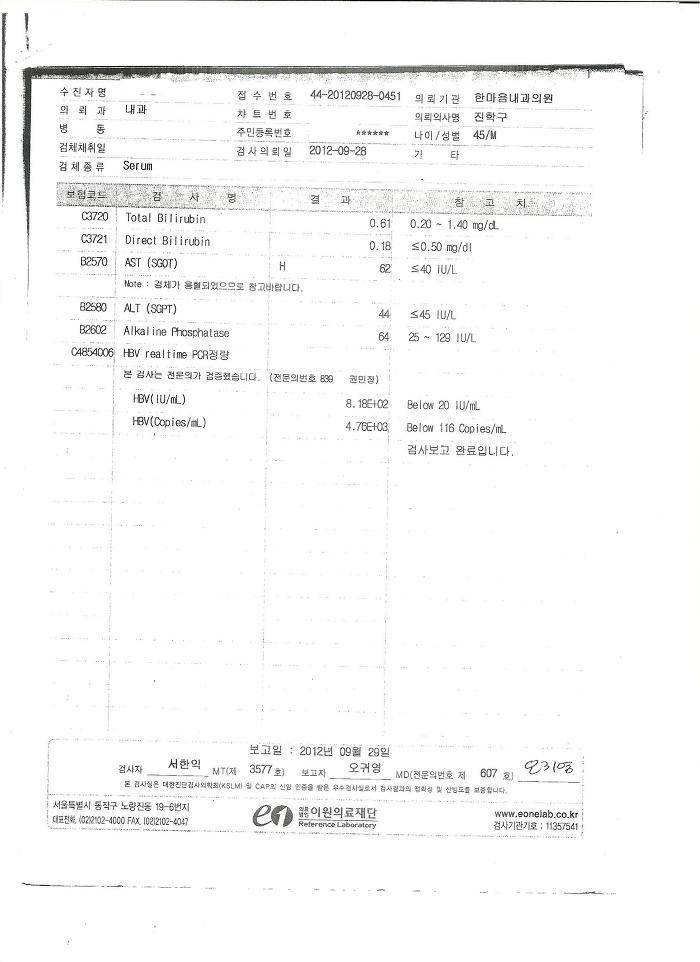
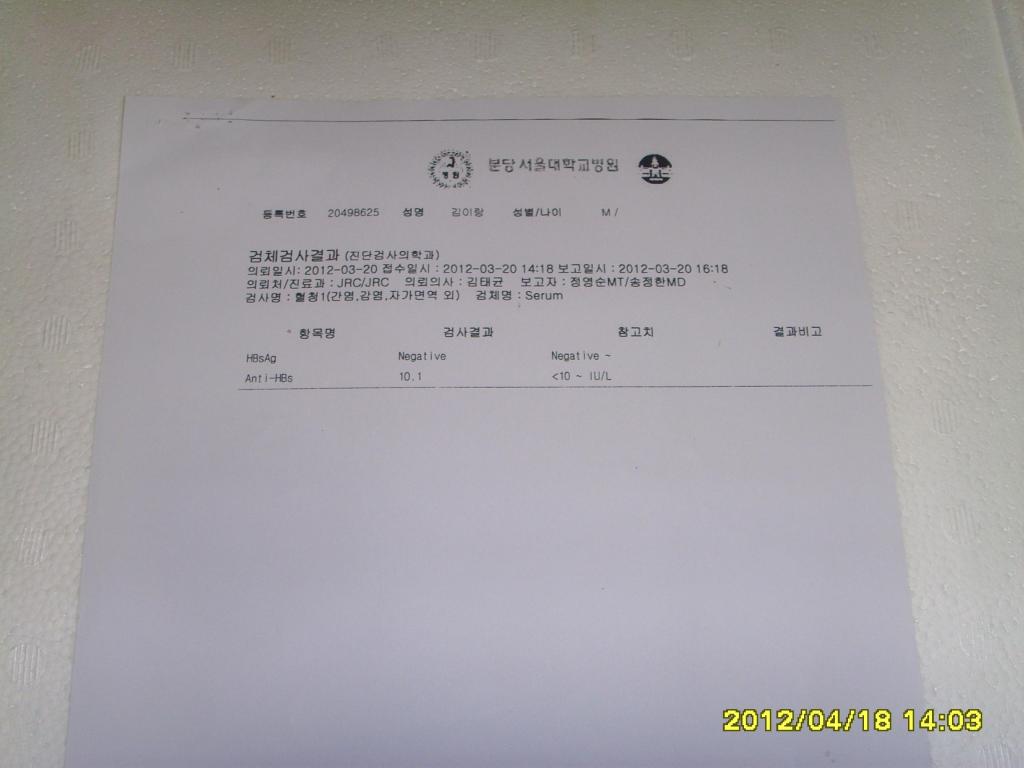
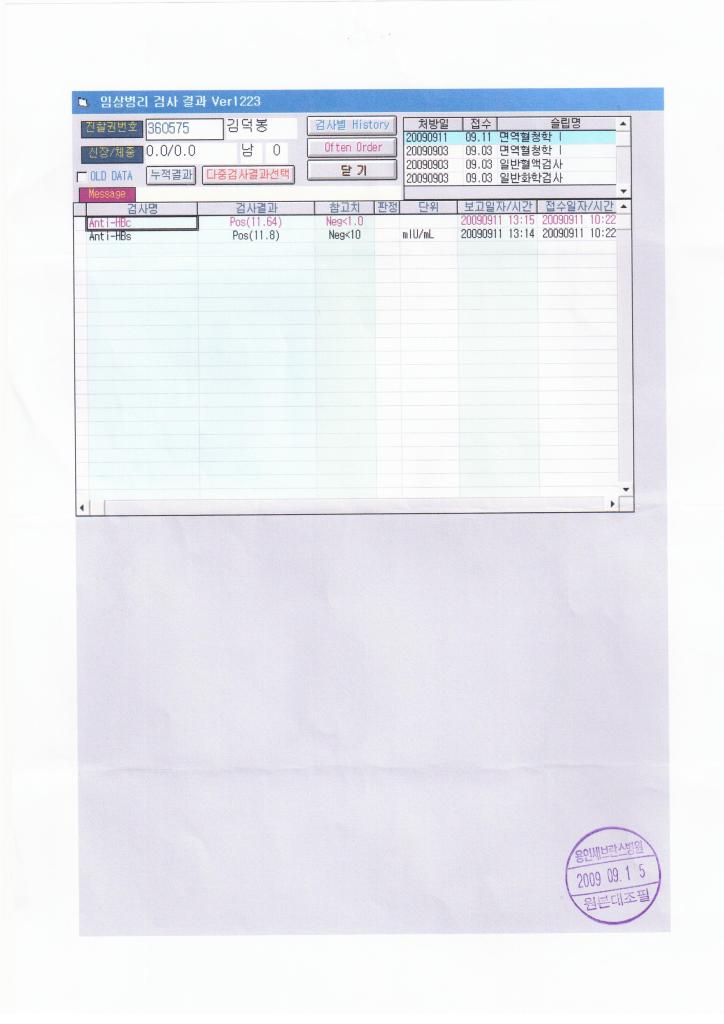
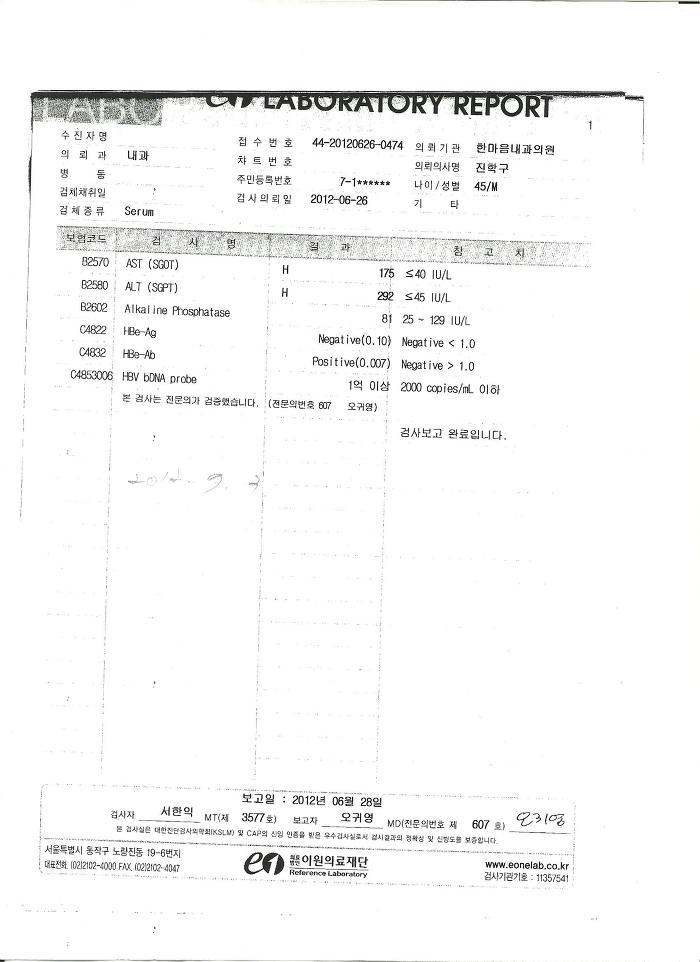
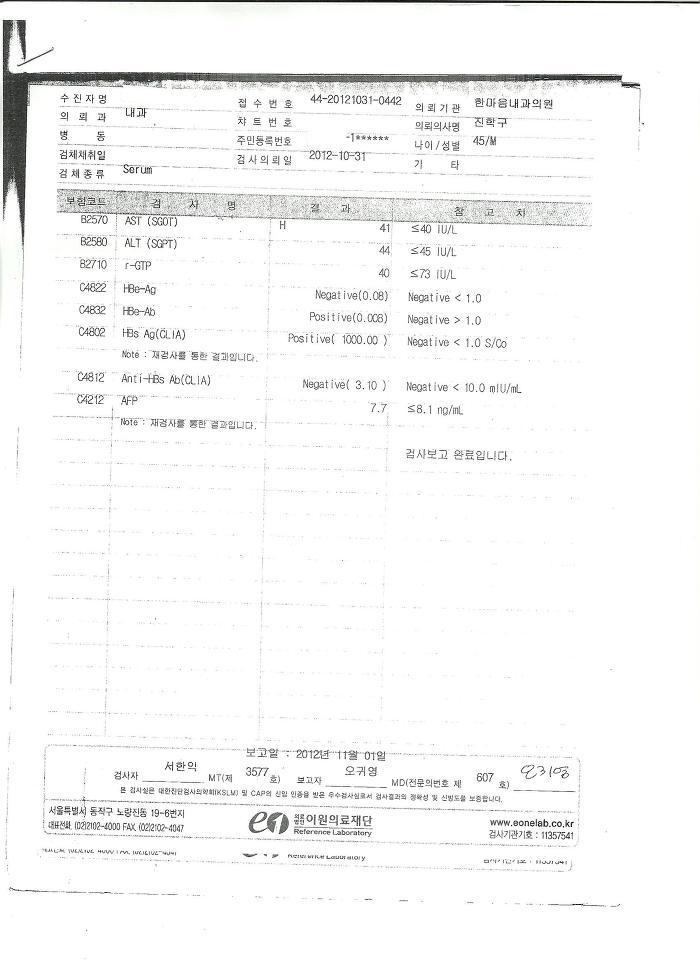
About a year ago I received an email from 주전골님 <sealhae@hanmail.net> about investing in North Korea. Below is the full context of the email as well as the JPG’s that were attached.
There’s nothing really interesting in the EXIF data other than the scanned documents have the phrase 형간염검사지 which apparently translates to hepatitis test papers. The only other piece of data that I’ve seen is on the picture with the timestamp in the bottom right corner. The picture was taken with a Digimax i6 PMP, Samsung #11 PMP
|
Internet Outages Solved
Looks like Wired got to the bottom of the recent outages in North Korea: https://www.wired.com/story/north-korea-hacker-internet-outage/
Now that it doesn’t make much of a difference this was a graph that I created a few days ago to start getting a better idea of when launches and outages were occurring.
As as side note to all of this I’ve spent far too much time in the last few days really digging into North Korea’s internet and the way that they are peering with other networks which probably will require a new post later.
GitHub Commits From Pyongyang University of Science and Technology (PUST)
PUST maintains a GitHub account for committing changes to open source projects on GitHub: https://github.com/arirang-pust
A sample commit can be found here: https://github.com/mlpack/mlpack/pull/842
Chat logs from the MLPACK developers discussing the change from PUST: https://www.mlpack.org/irc/mlpack.20161220.html
Blog post from the professor at PUST discussing the changes: https://izbicki.me/blog/teaching-open-source-in-north-korea.html
Associated LinkedIn account for PUST can be found here: https://www.linkedin.com/in/arirang-pust-748483144/
Thanks to the person that submitted this over email!