For the past few months, I’ve been working on scans from a VPS against the North Korean IP space to watch as different sites come online. I’ve got a decent scan that runs now but still needs some work. Below is what I’ve found but there is still a lot more digging to be done on the sites, but I wanted to at least start getting this information online and work on categorizing it better later:
Default Red Hat server with an Apache test page.
Open ports for each host:
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
135/tcp filtered msrpc
139/tcp filtered netbios-ssn
445/tcp filtered microsoft-ds
593/tcp filtered http-rpc-epmap
3306/tcp open mysql
4444/tcp filtered krb524
6000/tcp open X11
The banner reported for them as well shows as Red Hat, as opposed to Red Star Linux, which show up in some of the other hosts scanned: Apache/2.2.15 (Red Hat)
Network Gear:
175.45.178.142
- OS Identifications: Cisco 831 switch or 1760 router (IOS 12.4)
- SSH Banner: SSH-1.99-Cisco-1.25
Websites:
175.45.178.178
This is one that I always keep coming back to whenever it appears online. It looks like it is a North Korean security tool of some kind. The only information that I’ve been able to gather is in the following:
# wget –no-check-certificate https://175.45.178.178
–2015-07-05 01:10:06– https://175.45.178.178/
Connecting to 175.45.178.178:443… connected.
WARNING: cannot verify 175.45.178.178’s certificate, issued by “/C=XX/ST=XX/L=XX/O=NeoTech/OU=Secure Team/CN=NetRadar/emailAddress=nsd@neotech.com”:
Self-signed certificate encountered.
WARNING: certificate common name “NetRadar” doesn’t match requested host name “175.45.178.178”.
HTTP request sent, awaiting response… 200 OK

http://rodong.rep.kp
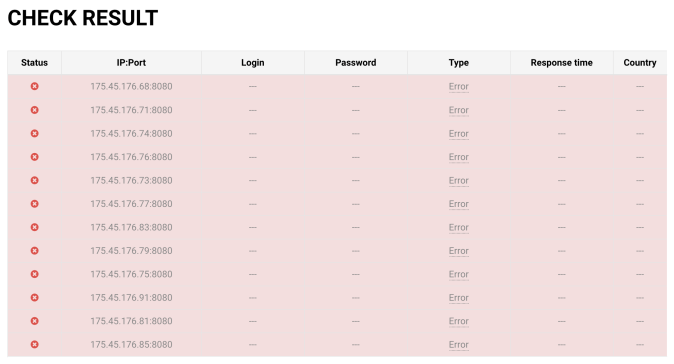
Depending on the country you are connecting in from you are Rodong will load from a different IP. Connecting from Romania produced 175.45.177.78 and Canada 175.45.176.68
Other than the fact that any picture of a crowd looks Photoshopped, you can also track Supreme Leaders activity. Site runs on Red Star 3.0: Apache/2.2.15 (RedStar 3.0)
http://kcna.kp
http://www.vok.rep.kp/CBC/
http://www.chosunexpo.com/expo_en/
Website of a software development company founded in 2002. Focuses on mobile and web apps, games, and applications.
175.45.176.67
There’s a lot of different domains for this address. It hosts a news site Naenara but there are several other domains associated with it as well:
175.45.176.79
Website of Kim Il Sung University. Haven’t had too much of a chance to dig into this site yet, seems pretty straightforward though.
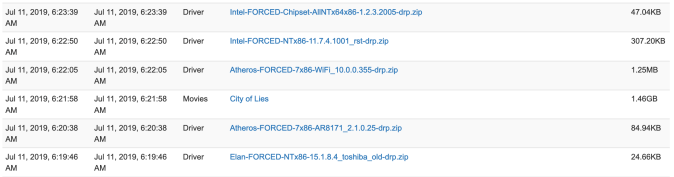
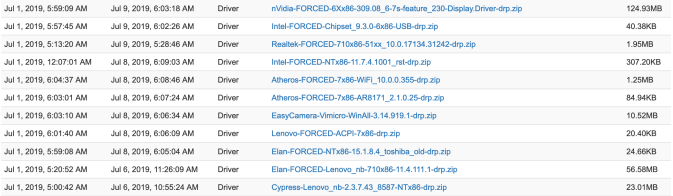
Scan results are below. Still working on tweaking the scan a little bit to get some more information.
7.14.15_nk