If you haven’t read part 1, you can read it here: https://nkinternet.com/2026/04/07/npm-malware-fake-devs-and-deepfake-videos-these-are-a-few-of-my-favorite-dprk-things/
In order to keep the first part of this short the plan was to break it into a series of smaller posts. However, within 7 days after publishing the last post most of the accounts were taken down. So what’s left and what accounts did they pivot to?
Mentonex Slack
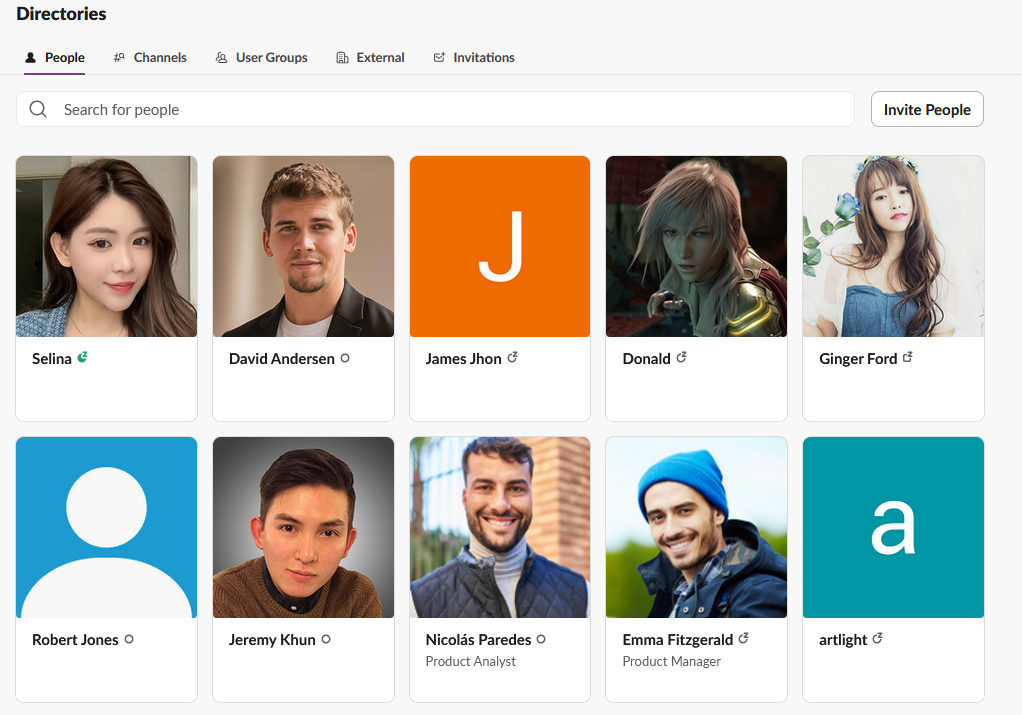
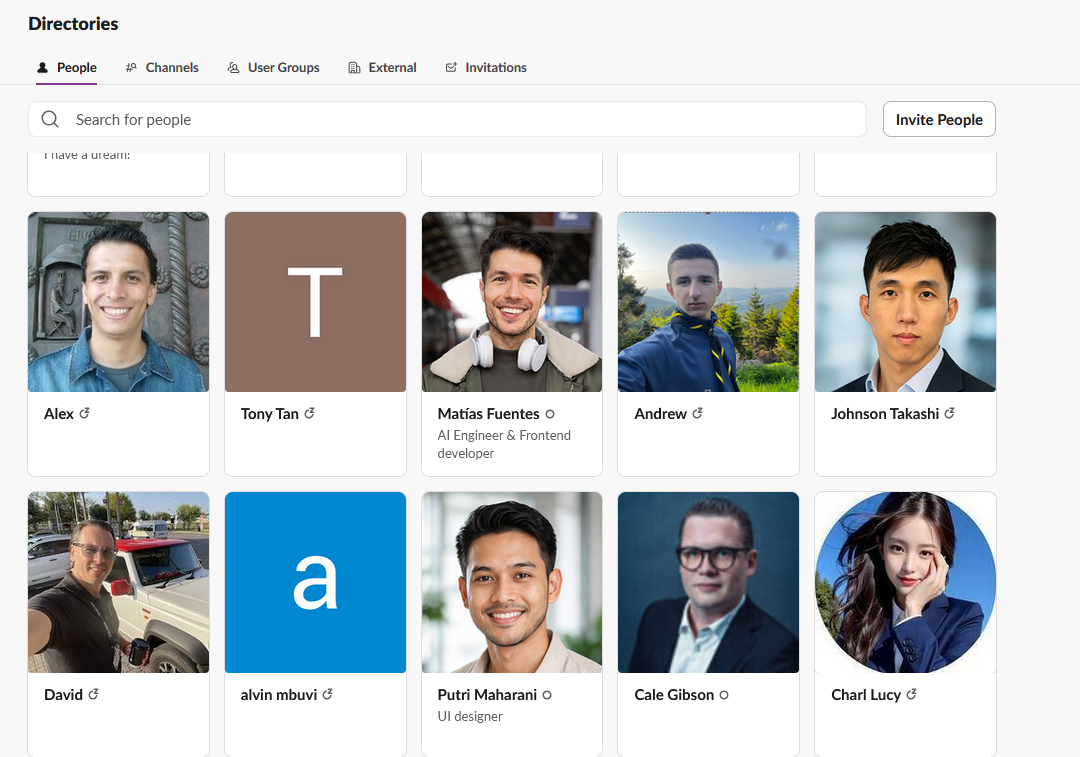
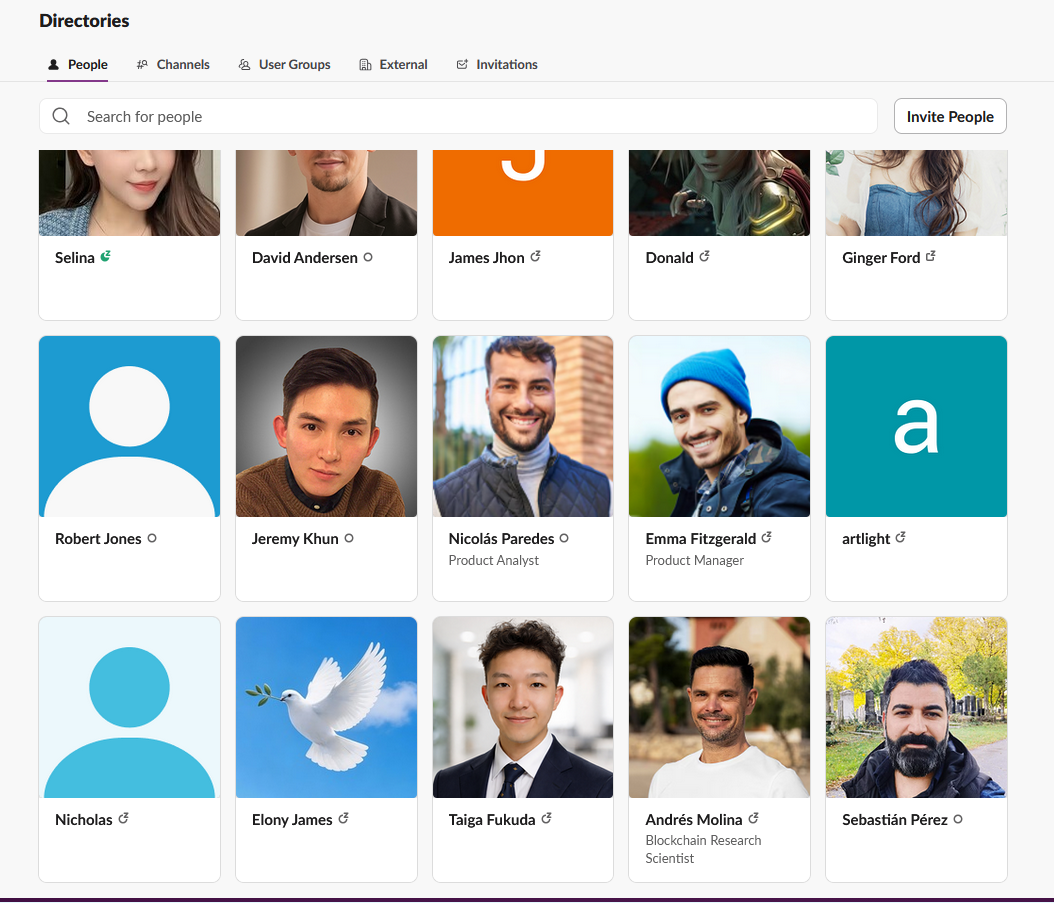
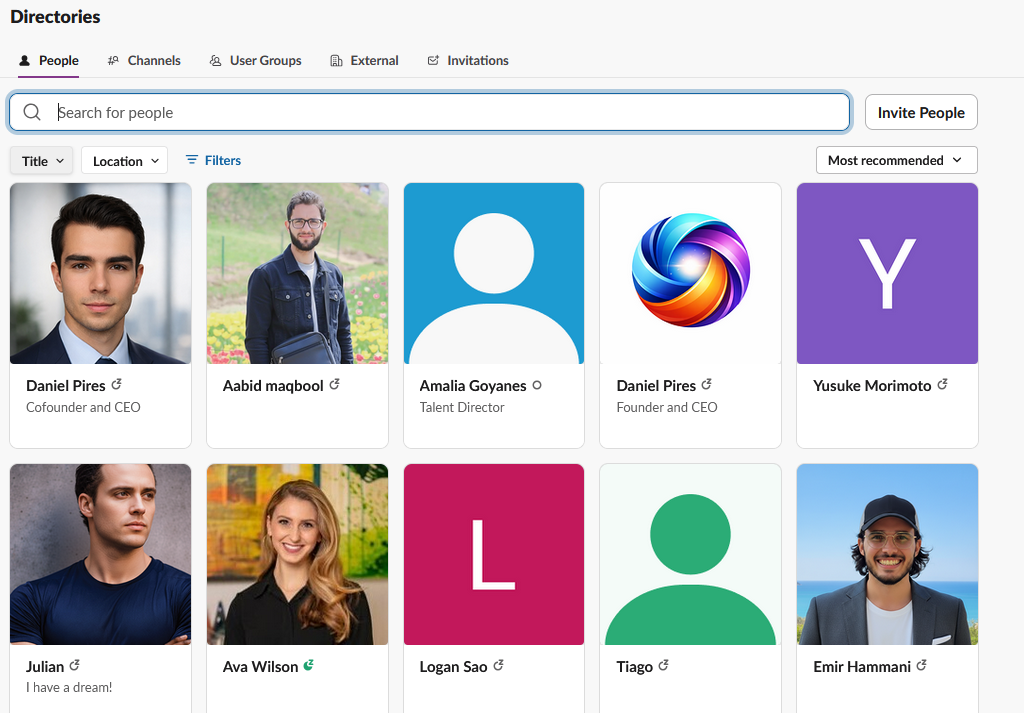
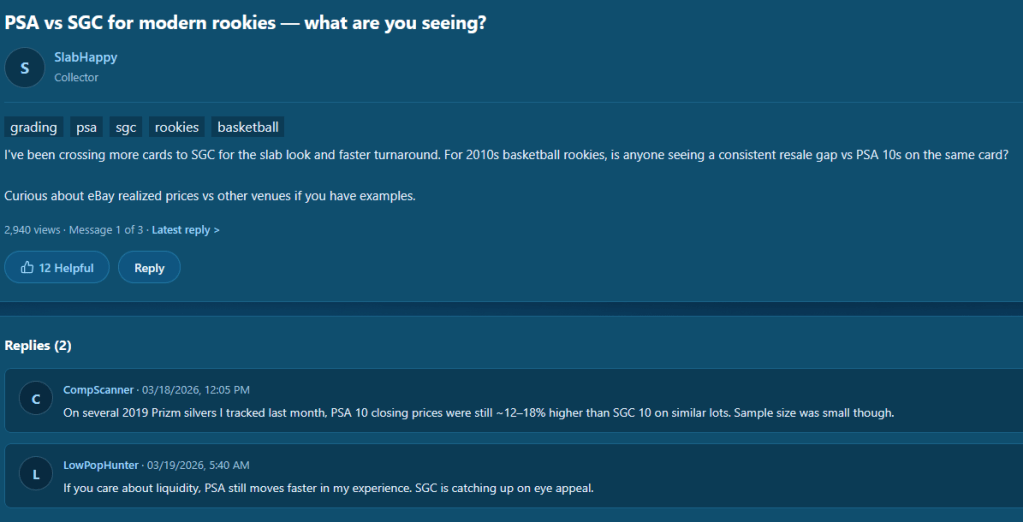
One thing that wasn’t included in the first post was screenshots of the Mentonex Slack channel. This was designed to appear to look like a legitimate company. There were messages posted about the company and a number of accounts that all appeared to be regular users.
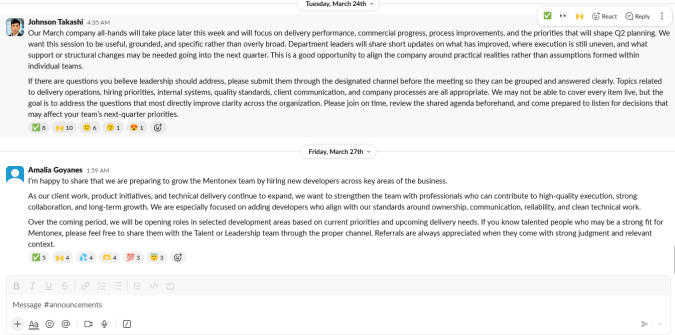
A list of users was also obtained. Several of them appeared to be copied from other legitimate users on LinkedIn. One profile of note is Charl Lucy who we’ll see more of in a few minutes.
This is a technique used by the DPRK on several occasions now. One noted example recently was the compromise of the npm package Axios:
Maintainer Jason Saayman said the attackers tailored their social engineering efforts “specifically to me” by first approaching him under the guise of the founder of a legitimate, well-known company.
“They had cloned the company’s founders’ likeness as well as the company itself,” Saayman said in a post-mortem of the incident. “They then invited me to a real Slack workspace. This workspace was branded to the company’s CI and named in a plausible manner. The Slack [workspace] was thought out very well; they had channels where they were sharing LinkedIn posts.”
https://thehackernews.com/2026/04/unc1069-social-engineering-of-axios.html
Pivoting Companies – A Wild Nixsora.com Is Discovered
Most of the profiles and companies mentioned in the last post appear to be offline or deleted. However this doesn’t mean we can’t find the new companies being created. A couple of small details lead to finding the new company pretty easily which is nixsora.com
A GitHuub user vexxloso was discovered that had connections to previous personas related to Mentonex. If you remember Charl Lucy from the previous Slack images, an account with the same picture was discovered for the GitHub user trader389 following vexxloso. Additionally the user walletdiscover1010-a11y who is still associated with Mentonex is also following vexxloso.
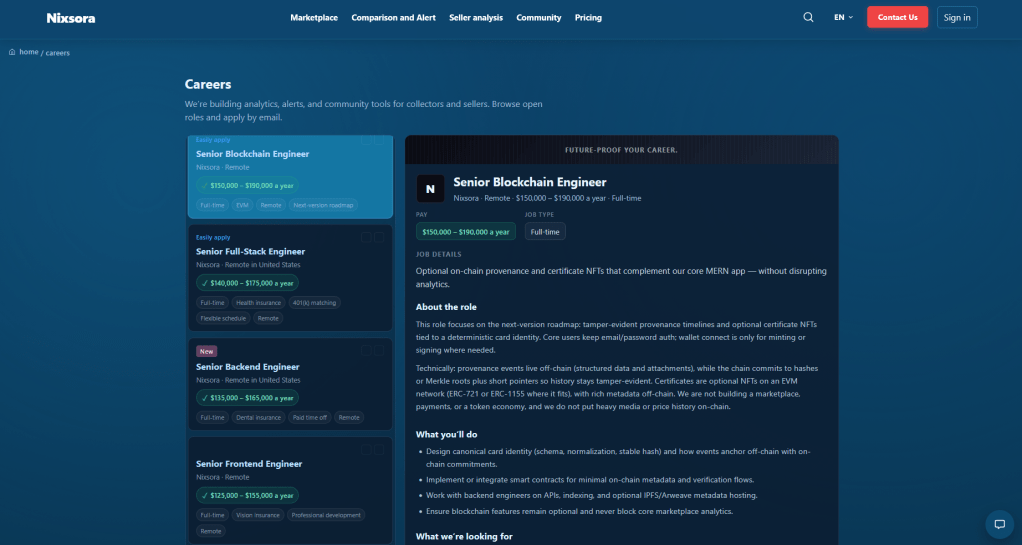
Looking at the job postings on nixsora.com reveals several posts looking to hire blockchain developers
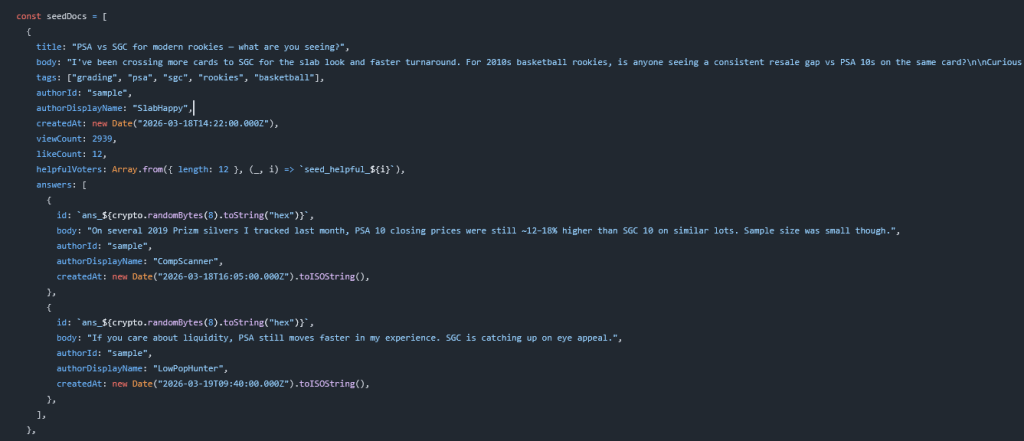
There’s also a community section on the website to make it appear as an active website but reviewing the code on GitHub shows that most of this is already seeded conversations into the pages.
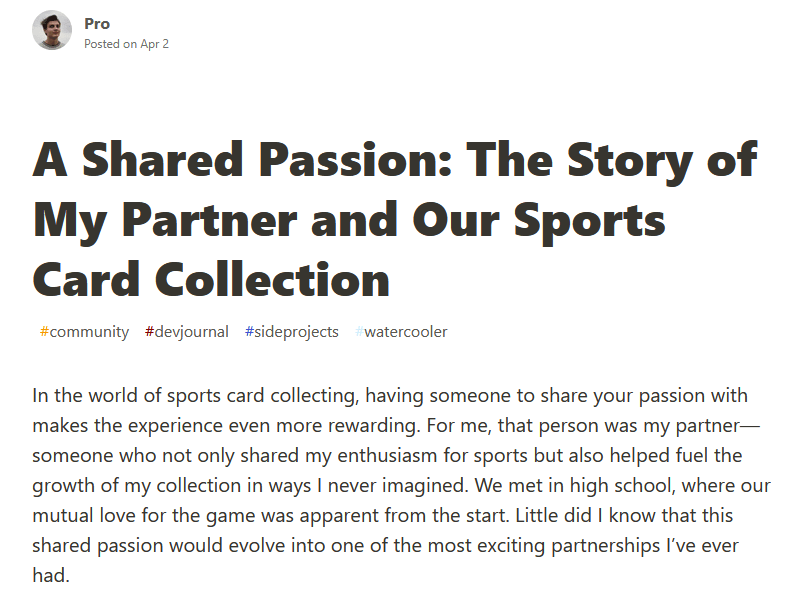
To further build credibility a persona James Jhon that shares a profile picture with vexxloso has been consistently posting on dev.to about their new sports card project
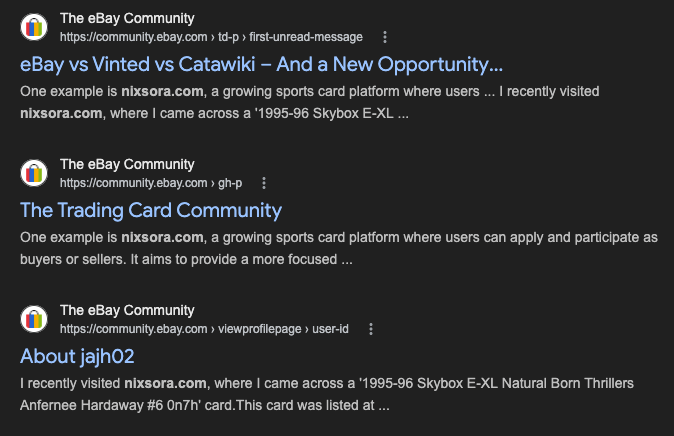
To build more credibility it appears that they are also posting about it in more legitimate spaces. While the pages appear to be removed, Google search results show several posts on eBay’s community page
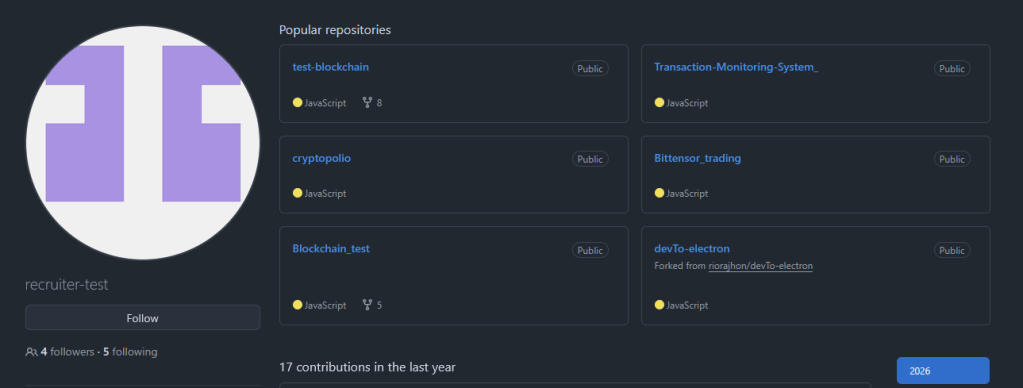
While no malicious code was discovered in any of the repositories, it does seem to be focused on part of a larger recruitment campaign. While pivoting on followers, another account tied to Nixsora, recruiter-test was discovered that has several blockchain related resting repositories.
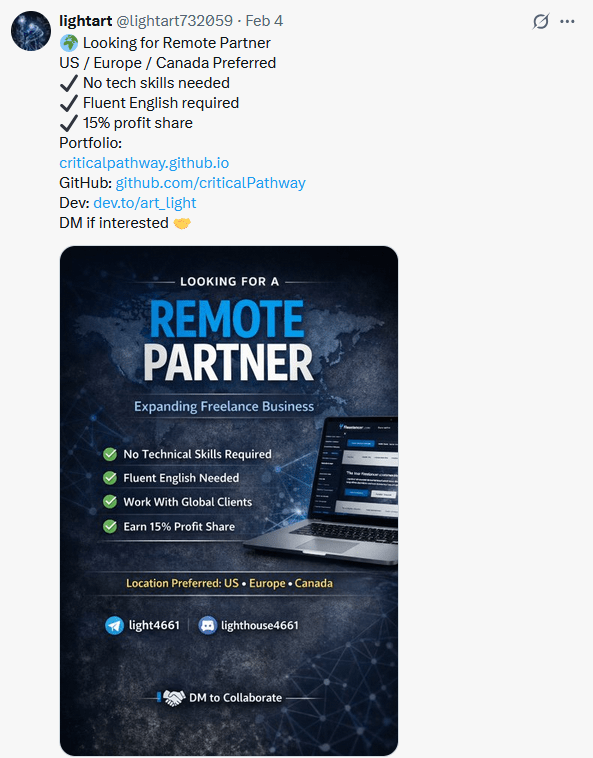
Another account associated with the cluster, lightart732059 was also posting online looking for remote workers to share profits.
Wrapping Up
A shorter post but interesting to see how the cluster of personas and companies evolve over time. Updates to the cluster will be posted as more emerge but I wanted to get the rest of my screenshots posted. This has also lead to the discovery of other interesting accounts such as NeuroPeakX who has a real time face swap repository, and riorajhon who shares a similar name previously observed that had a Dev.to repository forked by recruiter-test
Discover more from North Korean Internet
Subscribe to get the latest posts sent to your email.